Foram encontradas 481 questões.
READ TEXT AND ANSWER QUESTION:
Text
For the internal auditor, information technology is a two-edged sword. On the one hand, our survey shows that information systems have become tools to assist auditors in their day-to-day work; on the other hand, the rapid, continuing development of new information technologies causes continued worry about new auditing risks.
With the proliferation of portable computers and worldwide access through global networks, some auditing managers feel as if they are constantly under siege. "Security has been horrendous for us," states an internal auditing manager from a large agricultural corporation. "We have a lot of technology, but there is not a lot of internal control." This feeling of frustration was echoed by many of the survey's respondents.
Of greatest concern to internal auditors are the methodologies available to address modern information systems. The Internet looms as both an opportunity and a threat. Distributed databases raise new challenges for security and control. Image systems first used in the financial services community are being deployed more widely.
In short, the role of the internal auditor is changing. Partnership is a constant theme in our survey; internal auditing managers participate in business and information systems planning. According to an auditing manager from a major aerospace organization, "We will teach people to audit themselves and then check the checkers. We will be consultants and partners, and our job will increasingly be the training of others.
(http://www.theiia.org//index.cfm?doc_id=860 on July 12th, 2005)
The text indicates that information technology is:
Provas
READ TEXT AND ANSWER QUESTION:
TEXT
Vol. 8, July 1, 2005
Technology
What Organizations Should Know About VoIP - And Auditors Too
By Raquel S. Filipek
Editor, ITAudit
Many organizations are taking advantage of voice-over Internet protocol (VoIP) technology. Although there are great advantages to its use, auditors should understand the security risks posed by VoIP connections and help IT departments find ways to mitigate threats. |
Information technologies have revolutionized the way people communicate and work. Most computers are equipped with the latest versions of MSN Instant Messenger, Outlook Express, and other applications that facilitate data transfer and access. Wireless devices, such as cell phones, pagers, and personal handheld computers, are found everywhere and used by top-level executives and teenagers alike. Although it's taken a bit longer, telephones are finally joining the wireless club with VoIP - a technology that converts analog audio signals into digital data that is transmitted over the Internet. Digital data is then converted back into an analog signal, so users can speak with anyone using a regular phone.
The biggest draws to VoIP service are its economical price and flexibility. In the United States, phone and cable service providers are offering VoIP calling plans that are often better than cell phone plans, and government agencies, such as the U.S. Federal Communications Commission (FCC), are considering VoIP service as an alternative to traditional phone systems. However, VoIP is not perfect. The Cyber Security Industry Alliance (CSIA) - a public policy and advocacy group - recently published a report, Cyber Security for IP Telephony, that outlines several VoIP security recommendations the U.S. Congress should consider while revising the Telecommunications Act of 1996. As organizations become increasingly concerned over data theft and network security vulnerabilities, internal auditors need to assess the risks and advantages of switching to VoIP before organizations invest in this new technology.
(http://www.theiia.org/itaudit/index.cfm?fuseaction=forum&fid=5631)
According to the text, current computers are mostly:
Provas
READ TEXT AND ANSWER QUESTION:
TEXT
MSN Spam Postman Delivers Twice
By Sean Michael Kerner
May 26, 2005
As part of its spam fighting efforts, Microsoft today announced a pair of new services to help users and ISPs fight the deluge.
MSN Postmaster is a new online resource that Microsoft is making available globally in 10 different languages to help users and ISPs understand when and why MSN's popular Hotmail service considers an e-mail to be spam.
The Postmaster service provides a variety of tools and information resources that will help streamline the reporting of e-mail abuse, as well as improve the delivery of legitimate commercial e-mail messages.
Microsoft claims that its MSN Hotmail service has over 200 million user accounts worldwide and, as such, can provide a wealth of e-mail activity data.
The other new service announced today by Microsoft is Smart Network Data Services, which is currently just a preview release and only available in English.
The service is geared toward ISPs and reports on e-mail traffic characteristics sent from the ISP's IP range to Hotmail. The characteristics will help ISPs determine the volume of e-mail coming from under their auspices that is considered spam by the Hotmail service.
(www.internetnews.com/xSP/article.php/3508171)
The word twice in the title targets the:
Provas
READ TEXT AND ANSWER QUESTION:
Text
For the internal auditor, information technology is a two-edged sword. On the one hand, our survey shows that information systems have become tools to assist auditors in their day-to-day work; on the other hand, the rapid, continuing development of new information technologies causes continued worry about new auditing risks.
With the proliferation of portable computers and worldwide access through global networks, some auditing managers feel as if they are constantly under siege. "Security has been horrendous for us," states an internal auditing manager from a large agricultural corporation. "We have a lot of technology, but there is not a lot of internal control." This feeling of frustration was echoed by many of the survey's respondents.
Of greatest concern to internal auditors are the methodologies available to address modern information systems. The Internet looms as both an opportunity and a threat. Distributed databases raise new challenges for security and control. Image systems first used in the financial services community are being deployed more widely.
In short, the role of the internal auditor is changing. Partnership is a constant theme in our survey; internal auditing managers participate in business and information systems planning. According to an auditing manager from a major aerospace organization, "We will teach people to audit themselves and then check the checkers. We will be consultants and partners, and our job will increasingly be the training of others.
(http://www.theiia.org//index.cfm?doc_id=860 on July 12th, 2005)
The first sentence implies that technology:
Provas
READ TEXT AND ANSWER QUESTION:
TEXT
Vol. 8, July 1, 2005
Technology
What Organizations Should Know About VoIP - And Auditors Too
By Raquel S. Filipek
Editor, ITAudit
Many organizations are taking advantage of voice-over Internet protocol (VoIP) technology. Although there are great advantages to its use, auditors should understand the security risks posed by VoIP connections and help IT departments find ways to mitigate threats. |
Information technologies have revolutionized the way people communicate and work. Most computers are equipped with the latest versions of MSN Instant Messenger, Outlook Express, and other applications that facilitate data transfer and access. Wireless devices, such as cell phones, pagers, and personal handheld computers, are found everywhere and used by top-level executives and teenagers alike. Although it's taken a bit longer, telephones are finally joining the wireless club with VoIP - a technology that converts analog audio signals into digital data that is transmitted over the Internet. Digital data is then converted back into an analog signal, so users can speak with anyone using a regular phone.
The biggest draws to VoIP service are its economical price and flexibility. In the United States, phone and cable service providers are offering VoIP calling plans that are often better than cell phone plans, and government agencies, such as the U.S. Federal Communications Commission (FCC), are considering VoIP service as an alternative to traditional phone systems. However, VoIP is not perfect. The Cyber Security Industry Alliance (CSIA) - a public policy and advocacy group - recently published a report, Cyber Security for IP Telephony, that outlines several VoIP security recommendations the U.S. Congress should consider while revising the Telecommunications Act of 1996. As organizations become increasingly concerned over data theft and network security vulnerabilities, internal auditors need to assess the risks and advantages of switching to VoIP before organizations invest in this new technology.
(http://www.theiia.org/itaudit/index.cfm?fuseaction=forum&fid=5631)
One of the major threats to VoIP is its:
Provas
READ TEXT AND ANSWER QUESTION:
TEXT
Mediamatic/Special: Rambling Thoughts on Reality Engineering
How could you deal with the internet, master-infrastructure of our world, and totally escape from contemporary society? It's impossible. As soon as you think twice about computer technology, you end up thinking about how technology structures, shapes, engineers, designs society, your life, your interactions...
You all know the stories: the success of the peer-to-peer networks, the copyright issues that came from that and from the use of samples made easy by all the digitizing equipment. The sometimes horrifying stories concerning the regulating of the Internet; the spying possibilities built in software; the demand for better filtering. Or, on the other hand, the success of Open Source and Linux. You cannot but ask the question - also if you don't understand a lot about computers -: wait a minute, how do we want to work with this, how do we want to organize this world?
Working in this field, you end up talking and thinking about questions concerning standards, protocols - how are they designed and how should they be designed? How open are the standards and protocols, what do they allow and what not? And since you're not only dealing with the building blocks of your computer and your own little network, but with the protocols that shape or engineer the basic infrastructure of contemporary society, you get to the question: how's the Reality engineered by these protocols, these standards, this software, this infrastructure? What exactly is the connection between protocols and society? How should we conceptualize that interaction?
(http://www.mediamatic.net/article-200.6007.html&q_keyword=200.194)
The title implies that the thoughts in the text will be:
Provas
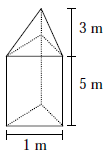
Um monumento de granito foi projetado no formato da figura abaixo: um prisma reto cuja base é um triângulo eqüilátero com uma pirâmide no topo. O lado do triângulo da base é 1m, a altura do prisma é 5m e a altura da pirâmide é 3m. O volume de granito necessário para a construção desse monumento será de:
Provas
!$ \begin{cases} 4x+my=4 \\ mx+9y=b \end{cases} !$
Valores de m e b que tornam o sistema possível e indeterminado são:
Provas
Unem-se os pontos médios de um quadrado de lado 1 obtendo-se um novo quadrado. Unem-se então os pontos médios desse segundo quadrado obtendo-se um terceiro e, assim por diante, indefinidamente.
A soma dos perímetros de todos esses quadrados é:Provas
No triângulo ABC , !$ \hat {A} !$ = 90º e AD é a altura relativa ao lado BC. Sabendo-se que BD = 2 cm e AD = 4 cm , o valor de CD, em centímetros, é:
Provas
Caderno Container