Foram encontradas 629 questões.
Assinale a alternativa que apresenta os elementos do trabalho de asseguração.
Provas
Os papéis de trabalho de auditoria são formalmente chamados de
Provas
O indivíduo que possui experiência prática de auditoria e conhecimento razoável de processos de auditoria, normas de auditoria e exigências legais e regulamentares aplicáveis, ambiente de negócios em que opera a entidade e assuntos de auditoria e de relatório financeiro relevantes ao setor de atividade da entidade é um
Provas
Observe a imagem a seguir.
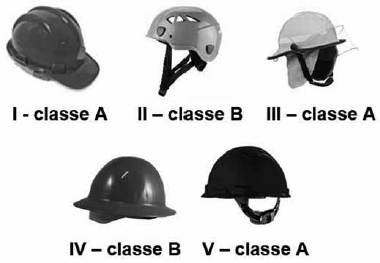
O capacete é um dos equipamentos de proteção individual mais importantes. Entre os modelos apresentados, o mais adequado para serviços em eletricidade é o indicado em:
Provas
Leia o texto para responder à questão.
The concept of virtual memory in computer architecture
Virtual memory is a technique used in computer architecture to make it appear as if the computer has more memory than it physically possesses. This is achieved by employing a combination of hardware and software mechanisms that manage the allocation and deallocation of memory resources. The primary aim of virtual memory is to enable efficient and seamless execution of programs and multitasking by allowing them to access more memory than what is physically available.
The concept of virtual memory was introduced to overcome the limitations of physical memory, such as the insufficient allocation of memory resources for large-scale applications. Virtual memory achieves this goal by providing a layer of abstraction between the physical memory and the running programs, allowing them to access a larger memory space than physically available.
At its core, virtual memory utilises a concept called “paging”, which divides the memory into fixed-size blocks called pages. These pages can then be stored in either physical memory or secondary storage devices, such as hard drives (HDs) or solid-state drives (SSDs). The process of managing these pages and mapping them to physical memory is handled by the Memory Management Unit (MMU) within a computer system.
(www.studysmarter.co.uk/explanations/computer-science
/computer-organisation-and-architecture/virtual-memory/)
O trecho do terceiro parágrafo “which divides the memory into fixed-size blocks called pages”, em relação a “paging”, apresenta uma
Provas
Leia o texto para responder à questão.
The concept of virtual memory in computer architecture
Virtual memory is a technique used in computer architecture to make it appear as if the computer has more memory than it physically possesses. This is achieved by employing a combination of hardware and software mechanisms that manage the allocation and deallocation of memory resources. The primary aim of virtual memory is to enable efficient and seamless execution of programs and multitasking by allowing them to access more memory than what is physically available.
The concept of virtual memory was introduced to overcome the limitations of physical memory, such as the insufficient allocation of memory resources for large-scale applications. Virtual memory achieves this goal by providing a layer of abstraction between the physical memory and the running programs, allowing them to access a larger memory space than physically available.
At its core, virtual memory utilises a concept called “paging”, which divides the memory into fixed-size blocks called pages. These pages can then be stored in either physical memory or secondary storage devices, such as hard drives (HDs) or solid-state drives (SSDs). The process of managing these pages and mapping them to physical memory is handled by the Memory Management Unit (MMU) within a computer system.
(www.studysmarter.co.uk/explanations/computer-science
/computer-organisation-and-architecture/virtual-memory/)
No trecho do segundo parágrafo “such as the insufficient allocation of memory resources for large-scale applications”, o termo destacado em negrito pode ser substituído, sem alteração de sentido, por
Provas
Leia o texto para responder à questão.
The concept of virtual memory in computer architecture
Virtual memory is a technique used in computer architecture to make it appear as if the computer has more memory than it physically possesses. This is achieved by employing a combination of hardware and software mechanisms that manage the allocation and deallocation of memory resources. The primary aim of virtual memory is to enable efficient and seamless execution of programs and multitasking by allowing them to access more memory than what is physically available.
The concept of virtual memory was introduced to overcome the limitations of physical memory, such as the insufficient allocation of memory resources for large-scale applications. Virtual memory achieves this goal by providing a layer of abstraction between the physical memory and the running programs, allowing them to access a larger memory space than physically available.
At its core, virtual memory utilises a concept called “paging”, which divides the memory into fixed-size blocks called pages. These pages can then be stored in either physical memory or secondary storage devices, such as hard drives (HDs) or solid-state drives (SSDs). The process of managing these pages and mapping them to physical memory is handled by the Memory Management Unit (MMU) within a computer system.
(www.studysmarter.co.uk/explanations/computer-science
/computer-organisation-and-architecture/virtual-memory/)
De acordo com o texto, o objetivo da memória virtual é
Provas
Leia o texto para responder à questão.
Information Security (InfoSec) defined
Information security, often abbreviated InfoSec, is a set of security procedures and tools that broadly protect sensitive enterprise information from misuse, unauthorized access, disruption, or destruction. InfoSec encompasses physical and environmental security, access control, and cybersecurity. It often includes technologies like cloud access security brokers (CASB), deception tools, endpoint detection and response (EDR), and security testing for DevOps (DevSecOps), among others.
Key elements of information security
InfoSec comprises a range of security tools, solutions, and processes that keep enterprise information secure across devices and locations, helping to protect against cyberattacks or other disruptive events.
• Application security - Policies, procedures, tools, and best practices enacted to protect applications and their data.w
• Cloud security - Policies, procedures, tools, and best practices enacted to protect all aspects of the cloud, including systems, data, applications, and infrastructure.
• Cryptography - An algorithm-based method of securing communication meant to ensure only intended recipients of a specific message can view and decipher it.
• Disaster recovery - A method to reestablish functional technological systems in the wake of an event like a natural disaster, cyberattack, or another disruptive event.
• Incident response - An organization’s plan for responding to, remediating, and managing the aftermath of a cyberattack, data breach, or another disruptive event.
• Infrastructure security - Security that encompasses an organization’s entire technological infrastructure, including both hardware and software systems.
• Vulnerability management - The process an organization takes to identify, assess, and remediate vulnerabilities in its endpoints, software, and systems.
Three pillars of information security: the CIA triad
Confidentiality, integrity, and availability make up the cornerstones of strong information protection, creating the basis for an enterprise’s security infrastructure. The CIA triad offers these three concepts as guiding principles for implementing an InfoSec plan.
Confidentiality
Privacy is a major component of InfoSec, and organizations should enact measures that allow only authorized users access to information. Data encryption, multi-factor authentication, and data loss prevention are some of the tools enterprises can employ to help ensure data confidentiality.
Integrity
Enterprises must maintain data’s integrity across its entire lifecycle. Enterprises with strong InfoSec will recognize the importance of accurate, reliable data, and permit no unauthorized user to access, alter, or otherwise interfere with it. Tools like file permissions, identity management, and user access controls help ensure data integrity.
Availability
InfoSec involves consistently maintaining physical hardware and regularly completing system upgrades to guarantee that authorized users have dependable, consistent access to data as they need it.
(www.microsoft.com/en-ww/security/business/security-101/
what-is-information-security-infosec#:~:text=Information%20
security%2C%20often%20abbreviated%20(InfoSec,access%2C%20
disruption%2C%20or%20destruction. Adaptado.)
Leia a parte do texto Three pillars of information security: the CIA triad para responder à questão.
De acordo com a parte do texto Three pillars of information security: the CIA triard, é correto afirmar que:
Provas
Leia o texto para responder à questão.
Information Security (InfoSec) defined
Information security, often abbreviated InfoSec, is a set of security procedures and tools that broadly protect sensitive enterprise information from misuse, unauthorized access, disruption, or destruction. InfoSec encompasses physical and environmental security, access control, and cybersecurity. It often includes technologies like cloud access security brokers (CASB), deception tools, endpoint detection and response (EDR), and security testing for DevOps (DevSecOps), among others.
Key elements of information security
InfoSec comprises a range of security tools, solutions, and processes that keep enterprise information secure across devices and locations, helping to protect against cyberattacks or other disruptive events.
• Application security - Policies, procedures, tools, and best practices enacted to protect applications and their data.w
• Cloud security - Policies, procedures, tools, and best practices enacted to protect all aspects of the cloud, including systems, data, applications, and infrastructure.
• Cryptography - An algorithm-based method of securing communication meant to ensure only intended recipients of a specific message can view and decipher it.
• Disaster recovery - A method to reestablish functional technological systems in the wake of an event like a natural disaster, cyberattack, or another disruptive event.
• Incident response - An organization’s plan for responding to, remediating, and managing the aftermath of a cyberattack, data breach, or another disruptive event.
• Infrastructure security - Security that encompasses an organization’s entire technological infrastructure, including both hardware and software systems.
• Vulnerability management - The process an organization takes to identify, assess, and remediate vulnerabilities in its endpoints, software, and systems.
Three pillars of information security: the CIA triad
Confidentiality, integrity, and availability make up the cornerstones of strong information protection, creating the basis for an enterprise’s security infrastructure. The CIA triad offers these three concepts as guiding principles for implementing an InfoSec plan.
Confidentiality
Privacy is a major component of InfoSec, and organizations should enact measures that allow only authorized users access to information. Data encryption, multi-factor authentication, and data loss prevention are some of the tools enterprises can employ to help ensure data confidentiality.
Integrity
Enterprises must maintain data’s integrity across its entire lifecycle. Enterprises with strong InfoSec will recognize the importance of accurate, reliable data, and permit no unauthorized user to access, alter, or otherwise interfere with it. Tools like file permissions, identity management, and user access controls help ensure data integrity.
Availability
InfoSec involves consistently maintaining physical hardware and regularly completing system upgrades to guarantee that authorized users have dependable, consistent access to data as they need it.
(www.microsoft.com/en-ww/security/business/security-101/
what-is-information-security-infosec#:~:text=Information%20
security%2C%20often%20abbreviated%20(InfoSec,access%2C%20
disruption%2C%20or%20destruction. Adaptado.)
Leia a parte do texto Three pillars of information security: the CIA triad para responder à questão.
No trecho do item Availability “authorized users have dependable, consistent access to data as they need it”, o termo destacado em negrito pode ser substituído, sem alteração de sentido, por
Provas
Leia o texto para responder à questão.
Information Security (InfoSec) defined
Information security, often abbreviated InfoSec, is a set of security procedures and tools that broadly protect sensitive enterprise information from misuse, unauthorized access, disruption, or destruction. InfoSec encompasses physical and environmental security, access control, and cybersecurity. It often includes technologies like cloud access security brokers (CASB), deception tools, endpoint detection and response (EDR), and security testing for DevOps (DevSecOps), among others.
Key elements of information security
InfoSec comprises a range of security tools, solutions, and processes that keep enterprise information secure across devices and locations, helping to protect against cyberattacks or other disruptive events.
• Application security - Policies, procedures, tools, and best practices enacted to protect applications and their data.w
• Cloud security - Policies, procedures, tools, and best practices enacted to protect all aspects of the cloud, including systems, data, applications, and infrastructure.
• Cryptography - An algorithm-based method of securing communication meant to ensure only intended recipients of a specific message can view and decipher it.
• Disaster recovery - A method to reestablish functional technological systems in the wake of an event like a natural disaster, cyberattack, or another disruptive event.
• Incident response - An organization’s plan for responding to, remediating, and managing the aftermath of a cyberattack, data breach, or another disruptive event.
• Infrastructure security - Security that encompasses an organization’s entire technological infrastructure, including both hardware and software systems.
• Vulnerability management - The process an organization takes to identify, assess, and remediate vulnerabilities in its endpoints, software, and systems.
Three pillars of information security: the CIA triad
Confidentiality, integrity, and availability make up the cornerstones of strong information protection, creating the basis for an enterprise’s security infrastructure. The CIA triad offers these three concepts as guiding principles for implementing an InfoSec plan.
Confidentiality
Privacy is a major component of InfoSec, and organizations should enact measures that allow only authorized users access to information. Data encryption, multi-factor authentication, and data loss prevention are some of the tools enterprises can employ to help ensure data confidentiality.
Integrity
Enterprises must maintain data’s integrity across its entire lifecycle. Enterprises with strong InfoSec will recognize the importance of accurate, reliable data, and permit no unauthorized user to access, alter, or otherwise interfere with it. Tools like file permissions, identity management, and user access controls help ensure data integrity.
Availability
InfoSec involves consistently maintaining physical hardware and regularly completing system upgrades to guarantee that authorized users have dependable, consistent access to data as they need it.
(www.microsoft.com/en-ww/security/business/security-101/
what-is-information-security-infosec#:~:text=Information%20
security%2C%20often%20abbreviated%20(InfoSec,access%2C%20
disruption%2C%20or%20destruction. Adaptado.)
Leia a parte do texto Three pillars of information security: the CIA triad para responder à questão.
O(s) item(ns) que destaca(m) a necessidade de permissão de acesso a dados apenas aos usuários autorizados são
Provas
Caderno Container